How to protect your brand from eSignature phishing scams
Signing agreements electronically saves time and makes it easier for businesses to close sales contracts, open bank accounts, and apply for insurance without the need to meet face-to-face. However, some electronic signature services can also come with unexpected risks.
A number of cybersecurity groups and experts have issued warnings about eSignature scams and phishing attempts using Docusign to electronically sign documents. In fact, research from Kaspersky reveals a significant rise in phishing attacks that mirror legitimate Docusign requests, often with a PDF attachment and QR code that leads to a phishing website.
Here's how the attack functions: Cybercriminals register for a free Docusign account or take over someone else's account and upload a malicious file that then masquerades as a legitimate Docusign envelope. More recently, phishing scams include templates, making it even easier for bad actors to trick the unsuspecting recipient into believing they’re getting an authentic request for signature.
If these types of spoofing techniques reach your customers, it could lead to malware downloads (such as ransomware) and hackers exploiting customers’ identity and personal information.
In this blog, we review the strategy behind phishing scams and how a security-conscious eSignature solution can help prevent these kinds of attacks.
What is a phishing scam?
A phishing scam tricks people into clicking malicious links to download malware or provide confidential information to criminals. It is one of the most common and successful social engineering schemes globally, and it shows no sign of slowing down. This is especially true because it can be automated using realistic templates and executed in bulk at a much larger scale.
The rise of web service impersonation attacks, a type of phishing attack using a recognized brand, involves fake websites and emails, and now PDF attachments and QR codes, that prompt people to log in and unknowingly give up their credentials to criminals. After stealing user credentials, hackers can then log in to other services.
Because people tend to reuse the same login credentials across many online accounts, bad actors can run an automated program to test credentials against any number of web services and, when successful, use them to impersonate the victim and steal funds or sensitive information.
Scammers and phishers are opportunistic and will adapt to current events and seasonal business activity, like holiday scams or tax scams. One tactic is to mask malware with something as routine as an invoice or shipping notice. When credentials are reused for multiple accounts in an organization, compromise of those credentials can have even more severe implications.
Why cybercriminals use Docusign phishing scams
The rise in Docusign phishing scams is directly tied to the increased use of eSignatures. Scammers launch phishing attacks designed to mimic emails from recognized brands, such as Docusign, because of the widespread use of its brand across its eSignature service and email notifications. Software providers like Docusign are constantly attacked by scammers (2018, 2019, 2020, 2023, 2024, 2025), who send fake emails from the vendor’s electronic signature service.
How do phishing scams work?
Phishing scams that leverage an eSignature software usually mimic the same format. It starts with an attacker who sends an eSignature “envelope” to their target. The recipient receives an email inviting them to review and sign a document.
Under normal circumstances, the recipient would simply click the “review document” link and eSign the document. In a phishing attack, however, the email contains links to either a website (phishing site) that asks the recipient to enter personal and financial information, or a malicious document, which, if run, would download malware onto the recipient’s device.
Interestingly, phishing scams are evolving to trick users into engaging with malicious links from their mobile devices. This is done by the increased use of a PDF attachment with a QR code inside. Once scanned, it begins downloading malicious software or directing the victim to a phishing website where their information is harvested by criminals. This method tricks users into opening the malicious link not on their computers, but on their mobile devices where phishing URLs are harder to detect, and security software might not be installed.
If the recipient falls for the scam, the attacker could use this information to access their bank account, credit card portals, and other online services.
3 ways to defend against eSignature phishing attacks
1. Protect your brand & customers against phishing emails
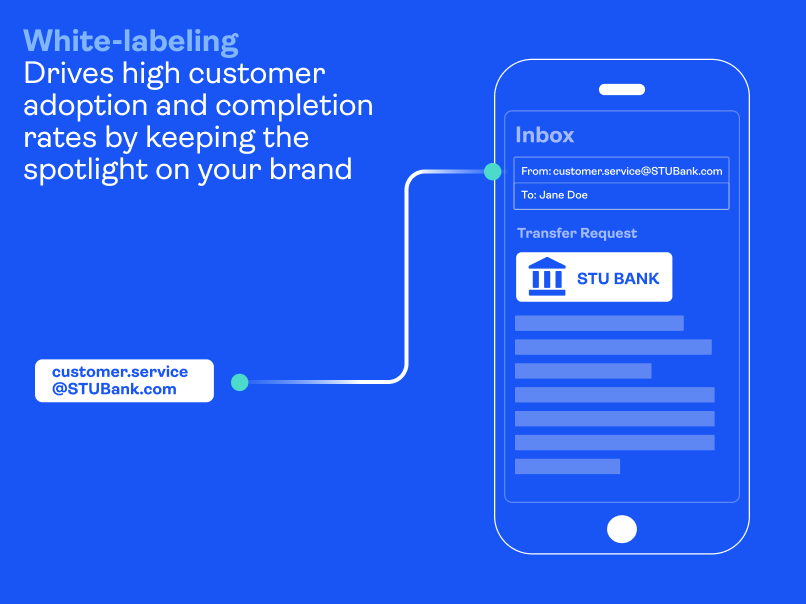
Docusign’s business model relies on a Docusign branding push using electronic signature notification emails. This puts its customers and their end-customers at risk of malicious attacks such as reported phishing scams mentioned above. That’s why it’s important to choose a solution that enables your organization to fully white-label the signing experience so your brand is front and center at all times.
White labeling is the top thing you can do to protect your brand, build trust with your signers, and achieve the highest completion rates. Growing awareness of deceitful phishing tactics – as well as the increase in programs educating people on email security – will dissuade recipients from trusting emails from third-party brands. If someone is expecting an eSignature invitation from their bank or insurance company, chances are they will more quickly delete such an email invitation if it comes from a service provider's email domain instead.
This is why it’s so important to fully brand the look and feel of email notifications and integrate the eSignature service with your email servers to allow emails to be sent from your domain (e.g., @yourbank.com) instead of the eSignature service’s domain. At OneSpan, we embrace this philosophy, and it’s a key reason why our OneSpan Sign solution is trusted by some of the most security-conscious brands in the world.
White-labeling tips to help prevent phishing attacks:
- Integrate the eSignature tool with your own email servers to allow emails to be sent from your domain (e.g., @yourbank.com), which is considered a trusted source
- Customize the content and look and feel of email notifications
- Customize the colors, logo, and the visibility of elements such as headers, navigation bars, footers, etc.
- Customize dialog boxes and error messages
2. Add enhanced authentication to secure access to your agreements
In addition to white labeling, businesses should never overlook security measures, such as ID verification and authentication. Multi-factor authentication (MFA), such as passkeys based on the FIDO standard, is one of the top ways to protect against phishing. Using strong authentication methods is a more powerful deterrent than single-factor email authentication alone.
OneSpan Sign offers a range of ID verification and authentication options as layers of protection for your high-value agreements, so you can get documents electronically signed with confidence. You have the flexibility to choose the level of security you need. This helps make sure your agreements are safely accessed and signed only by the individuals they’re intended for, with options including SMS, Q&A, knowledge-based authentication (KBA), passkeys, and government ID document checks.
3. Educate employees on how to spot a phishing email
Raise awareness among your employees that scammers will send phishing links through emails that appear to come from a well-known company, like Docusign. Let them know there are two key warning signs that the eSignature request is a scam:
- They are not expecting any documents to sign. If a business partner wants one of your employees to sign an agreement, it’s common practice for them to contact the employee first and let them know that a signature request is on its way. If an employee is not expecting the request to sign a document, advise them to report the email as a phishing scam and delete it. They should not click any hyperlinks or attachments.
- They notice an unusual sender or email domain. If an employee receives an unexpected eSignature request, they should always check the sender’s email domain. If the email isn’t coming from a legitimate business partner’s domain, it’s likely a scam.
In legal, HR, procurement, and finance departments, individuals often receive numerous documents that require signatures as part of their daily work processes. Due to the nature of their roles, an unsolicited email from Docusign may not arouse suspicion, especially if the email is well-crafted and appears to come from a seemingly legitimate sender. Criminals may exploit this by using compromised company domains or even sign up for free DocuSign accounts.
This is why it’s important to be mindful of other signs of a possible phishing scam, such as typos, misspellings, and grammar mistakes in the subject line or email body. These are common indicators that the email could be a phishing scam. Phishing emails may also use generic greetings since they are often used repeatedly or mass-emailed to a list of unsuspecting victims.
Building digital trust with employees and customers
From eSigning necessary employment forms to mortgage applications, electronic and digital signatures play an important part in our lives. Yet with the increased use of digital technologies and channels, there’s an increased risk of falling victim to threat actors’ malicious efforts. It’s likely that some of your employees and customers will be tricked into clicking on seemingly legitimate eSignature requests, entering their email credentials and handing them over to bad actors.
Issues around eSignature phishing attacks illustrate the importance of protecting your digital agreement processes. In all areas of our business, OneSpan is focused on enabling secure digital agreements and customer experiences. Review the capabilities of your electronic signature solution to ensure they include countermeasures like white labeling, strong authentication options, and document flattening. That way, your signers have greater protection against eSignature phishing scams.
See for yourself how OneSpan Sign inspires trust in today’s digital world.

