Software authentication: Modern apps and technology are a plus for customer loyalty, says Bank of Cyprus
This is the story of how Bank of Cyprus met PSD2 SCA requirements and enhanced the customer experience with integrated mobile authentication and PSD2-compliant dynamic linking (AKA transaction signing or transaction authorization). This blog is a summary of the full case study. Read the case study for additional details and insights from the bank, as well as workflow diagrams and video demos.
The Bank of Cyprus has distributed Digipass® hardware tokens to their customers for years. However, as customers shift to mobile transactions, the bank recently implemented software authentication and transaction-specific OTP one time passwords in compliance with the revised Payment Services Directive (PSD2).
Because of their hardware authenticators, the Bank of Cyprus was already compliant with the two-factor authentication (2FA) requirement for account login. However, the bank lacked software authentication capability. With approximately 50% of all digital banking transactions happening through mobile devices, this had become a pressing need. The bank had to find an easier and more convenient authentication mechanism where customers no longer needed to carry their hardware device(s) around with them.
Bank of Cyprus: The Challenge
The challenge for the bank was not replacing the hardware devices with software authentication. The real question was how to comply with one of the key requirements in PSD2: dynamic linking. The requirement to perform dynamic linking (also known as transaction signing or transaction authorization) to authenticate a financial transaction is one of the most discussed requirements of the PSD2 Regulatory Technical Standards (RTS) on Strong Customer Authentication (SCA) and Common and Secure Communication (CSC). Because the RTS is technology neutral, it does not prescribe a specific method for implementing dynamic linking. However, the RTS does specify that in the case of a payment transaction, the authentication code must be dynamically linked to the amount and payee, meaning that this code must change if either the amount or the payee is changed during the transaction. Additionally, payment information needs to be exchanged via a secure channel and must be clearly shown to the user.
The team knew that they needed to approach PSD2 not merely from a compliance point of view – they also had to optimize the user experience. The bank wanted to avoid a scenario where mobile-first customers would have to toggle between the Bank of Cyprus app and a separate authenticator app.
“From the day we wrote down the functional specifications with the cooperation of the bank’s IT Department and guidance from our Information Security Department, as well as other departments of the bank, the top requirement was that the software authenticator be fully integrated with the Bank of Cyprus mobile app,” says Toula Efthymiadou. Within the bank’s Digital Service Channels division, Toula leads the Business Solutions Department of the Digital Service Channels. She manages business development for the online banking, mobile app, and ATM channels, and is also responsible for the customer authentication technology.
“Offering a seamless customer experience was key,” she explains. “It was critical that PSD2 compliance not impose a burden on the customer.”
Bank of Cyprus: The Solution
After several consultations on the PSD2 RTS and demonstrations that confirmed OneSpan’s solutions complied with requirements, the Bank of Cyprus selected OneSpan’s software authentication, as well as the push notifications option and Cronto® visual transaction signing – all integrated through the SDKs in the OneSpan Mobile Security Suite.
For account login and dynamic linking, the bank decided to introduce software authentication integrated directly into the Bank of Cyprus mobile banking app. For customers who do not use the mobile banking app but still make online payments, the bank offers the ability to receive the OTP one-time password authentication code via SMS (online) or scan a Cronto code (offline).
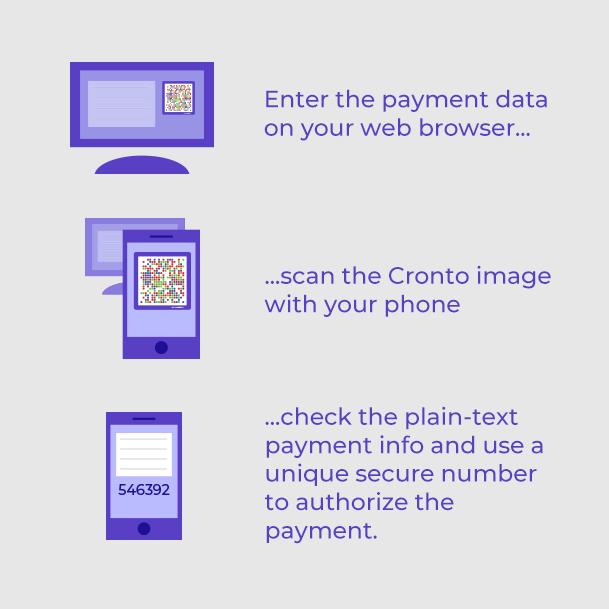
Cronto technology uses a colored cryptogram that represents the encrypted transaction data. When the user wants to initiate a transaction, they:
- Enter the payment data into the online banking application in the browser. The banking server then generates the colored cryptogram from the payment data and displays it in the browser.
- Scan the cryptogram using the camera of their mobile device. The device decodes the cryptogram, decrypts the payment data, and shows it to the user as clear text.
- Authenticate to their device, and it calculates the authentication code over the payment data using a cryptographic key stored on the device. (Note: Unlike other solutions, a Cronto cryptogram can only be read by an authorized user’s authorized device. The code cannot be read by just any device.)
This approach meets all dynamic linking requirements outlined in the PSD2 Regulatory Technical Standards.
Live in Pilot in 3 Months
The bank outsourced the integration with their mobile banking app and their IT team handled everything else.
“We anticipated a long implementation because on the business side, we put together a functional specifications document of 100 pages. It was very detailed and explained step-by-step exactly what we wanted the customer to experience in every scenario,” says Toula.
The IT team prioritized this project as high and started working on it intensively. As a result, the project went live (in pilot) in three months (October 2016 – January 2017). “Three months from the start of implementation to the go-live. We were amazed to be able to go live so quickly.”

Customer Adoption at 30-40% To Date
“Usage of the integrated authentication is at 30 – 40% to date. The people who have purchased it don’t want to go back to using a hardware device. Once they try the software authentication, they are very comfortable. It’s seamless and very easy to use.”
While the bank recommends that customers replace their hardware tokens with software authentication, many transactions are still signed (i.e., dynamically linked) using the OTP from hardware authenticators. “Mobile app usage is catching up, but the first customers using the software method are the tech-savvy segment,” says Toula. “From customer feedback through the call center, private individuals prefer the integrated software authentication experience. Overall, in terms of highest adoption, the software authentication is most preferred, followed by the Cronto code.”
As an added benefit, customers perceive the Bank of Cyprus as modern because the bank is enabling technologies like Touch ID and FaceID. “It’s things like having Touch ID or FaceID on the device that reinforces Bank of Cyprus as being a leader in the market. The software authentication also enhanced this perception. When we introduced it, we received positive comments from customers. Having new, modern applications and technology is a plus for customer loyalty.”

