Digital Agreements blog
News, trends, and expert perspectives on digital agreements and secure eSignatures.

Digital agreement innovations: OneSpan H1 2026 enhancements
From new workflow automation capabilities to customer experience improvements and stronger identity verification, our latest OneSpan Sign digital agreement innovations are designed with your organization in mind.

OneSpan Sign: Delivering digital trust in a changing world
The eSignature Newsletter for April 2026
Use cases
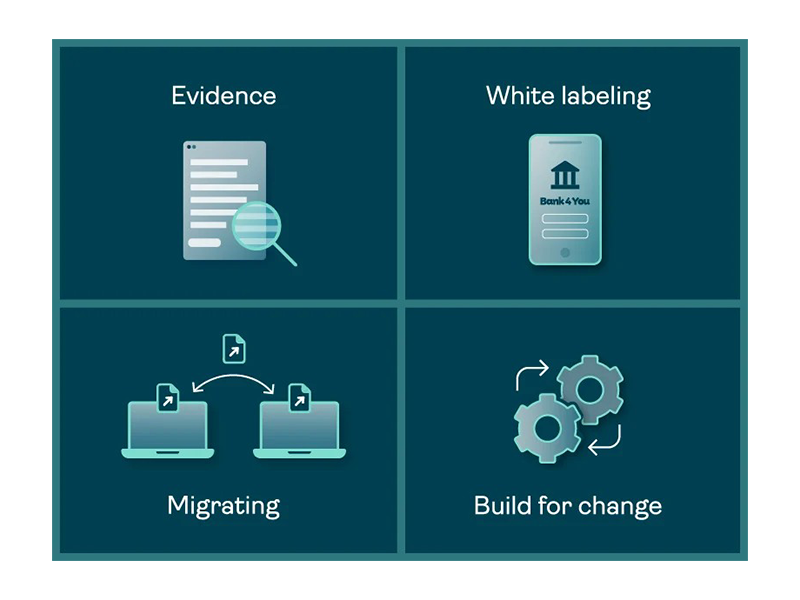
Four ways financial services can build trust into digital agreements

Use cases
Digital agreement innovations: OneSpan H1 2026 enhancements

Market insights
6 telltale signs it’s time to switch eSignature providers
Market insights
The eSignature Newsletter for April 2026

eSignature
OneSpan Sign: Delivering digital trust in a changing world
Compliance
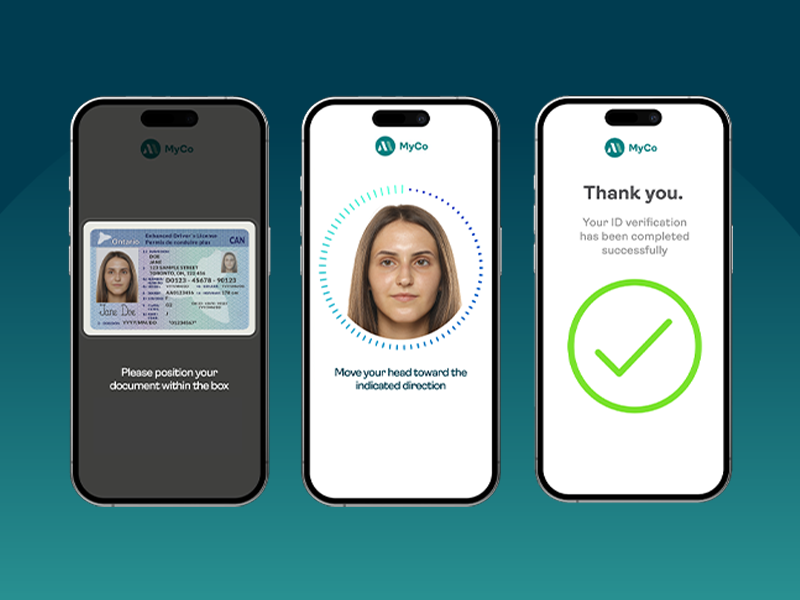
FINTRAC: Preparing your identity verification strategy for more than just compliance

Compliance
FINTRAC’s identity verification guidance is a timely step forward—but compliance will require legwork
Market insights
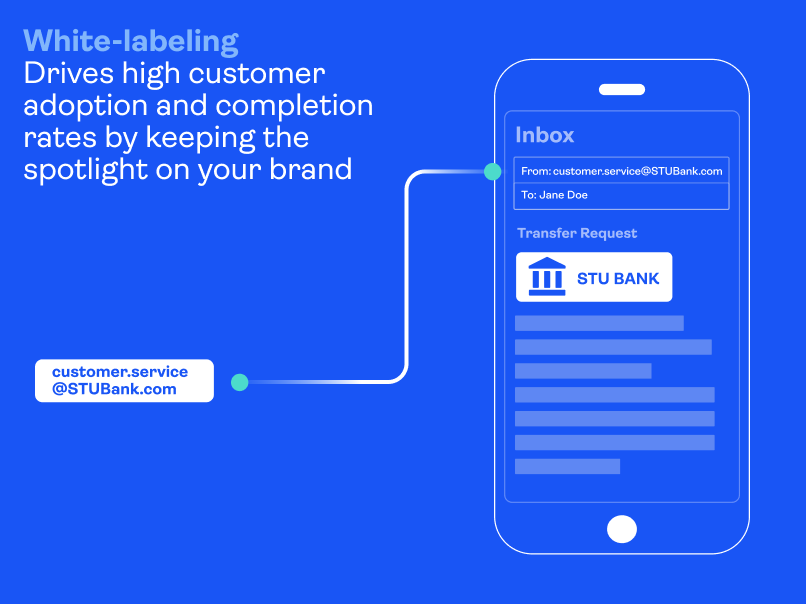
How to protect your brand from eSignature phishing scams

Use cases