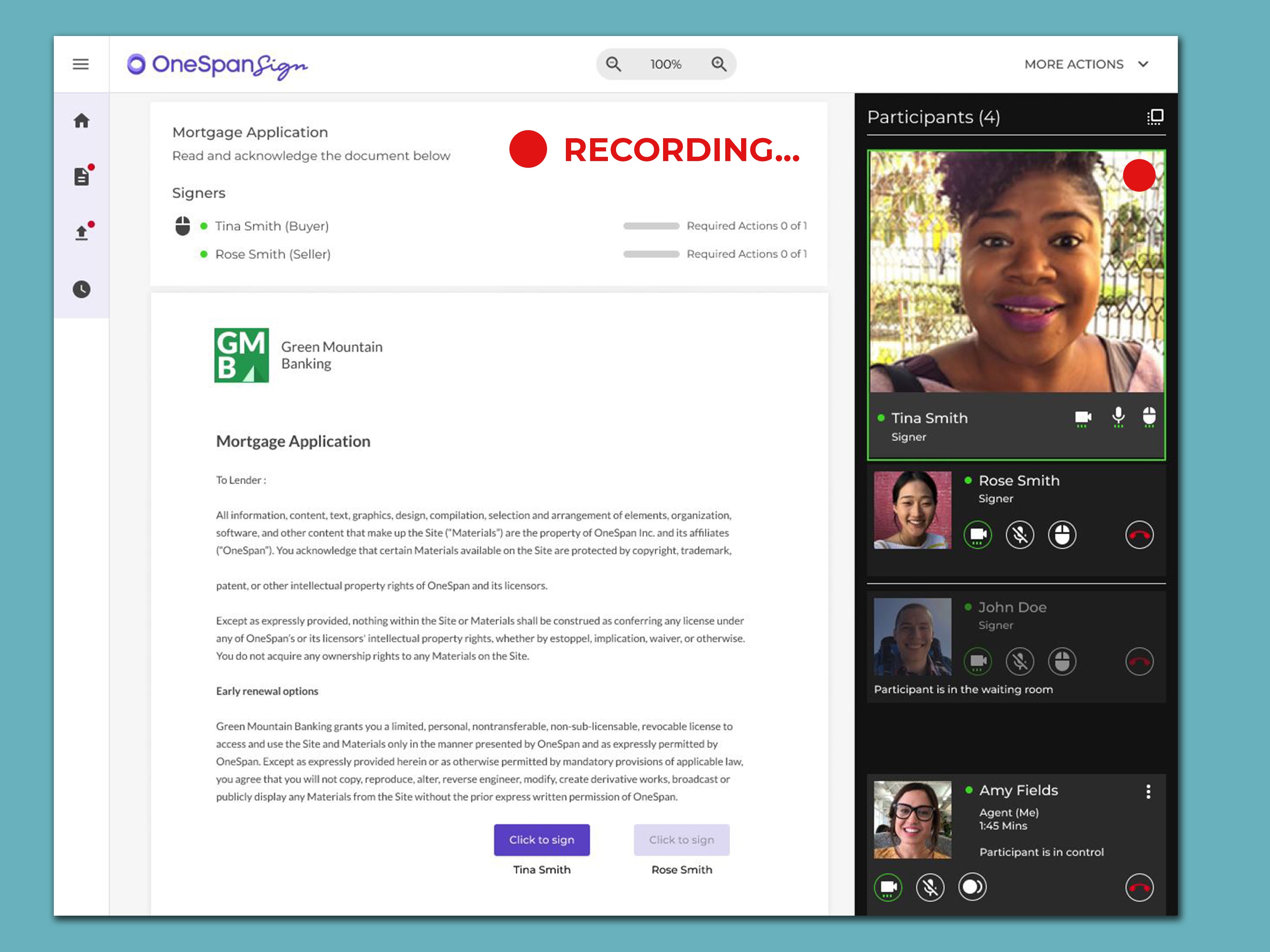
OneSpan Sign Developers: Virtual Room Recording – Part 2
Picking up where we left there, in this blog, we will showcase how the host can be notified when video...
3 Key Requirements for the Best Passwordless Authentication Solutions
The best passwordless authentication solutions can address three key challenges. Learn how best to...
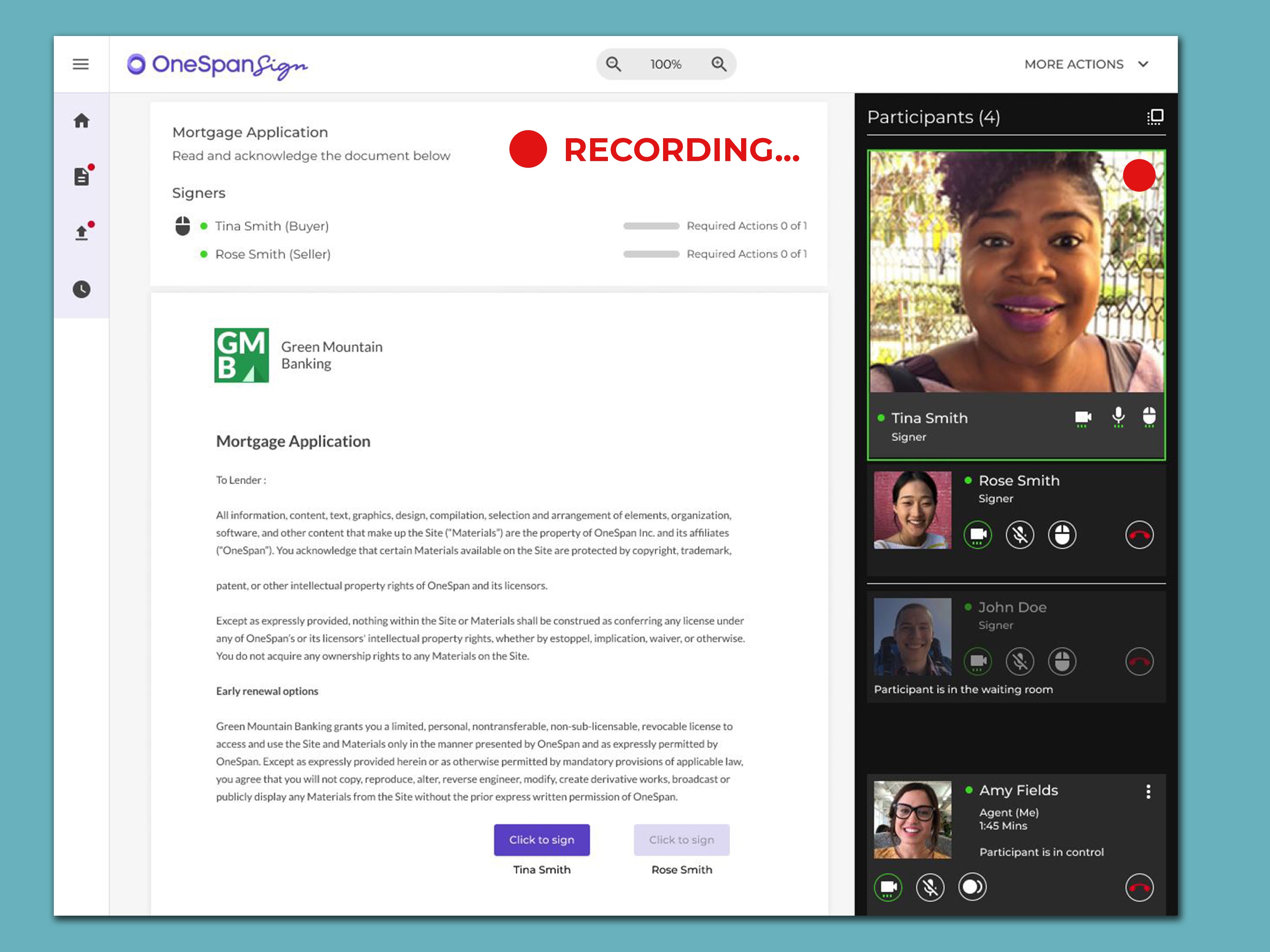
OneSpan Sign Developers: Virtual Room Recording – Part 1
OneSpan Sign Virtual Room (VR) offers vendor-independent audit trails with the option to capture a video...
Using E‑Signatures to Ensure Business Continuity in an Increasingly Digital World
E-signatures play a crucial role in digitising processes across organisations, but there are still a lot...
Readiness Checklist: How to Get Started with E‑Signatures Right Now
Explore how to implement electronic signatures as well as the top technical requirements and a useful...
Phishing: Attackers Use E‑Signature Software to Send Emails with Malicious Links
Defend against DocuSign phishing scams and other social engineering attacks that mimic messages from...
How Attackers Bypass Modern Two-factor Authentication and How to Protect Your Users
Learn how hackers are bypassing two-factor authentication using this technique and how to counter it.

OneSpan Sign Developer: 2022 SDK Updates
As OneSpan Sign rolls out new releases, we’ve added exciting new features. Let’s walk through recent SDK...
